Resource Center
What you need to know about how Axon Evidence and body-worn camera systems work
:format(webp))
As digital evidence becomes more central to the justice process, there has been growing interest in understanding how Axon’s body-worn cameras and digital evidence systems operate—specifically how video is stored, how user actions are tracked, and what happens to footage over time. These are important questions, and we welcome the chance to outline the processes involved.
Axon builds technology to support public safety professionals with a focus on security, accountability, and transparency. Our role is to provide secure tools, safeguards, and compliance frameworks, but how those tools are used is ultimately up to each agency. Here is what that looks like in practice.
A platform built for traceability and chain of custody
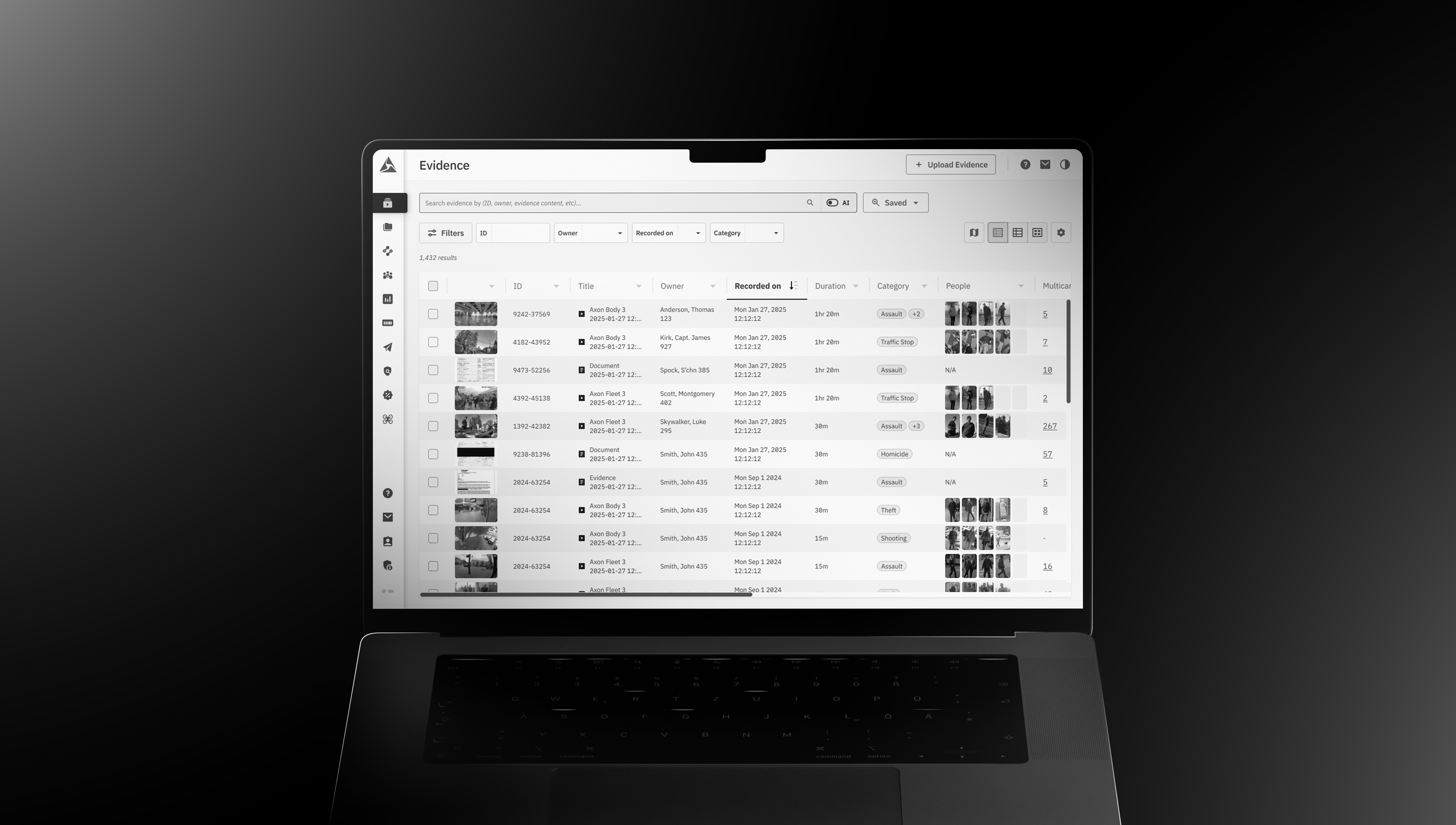
Axon Evidence is a secure, cloud-based system that helps law enforcement agencies store, manage, and review digital evidence, including videos captured on body-worn cameras.
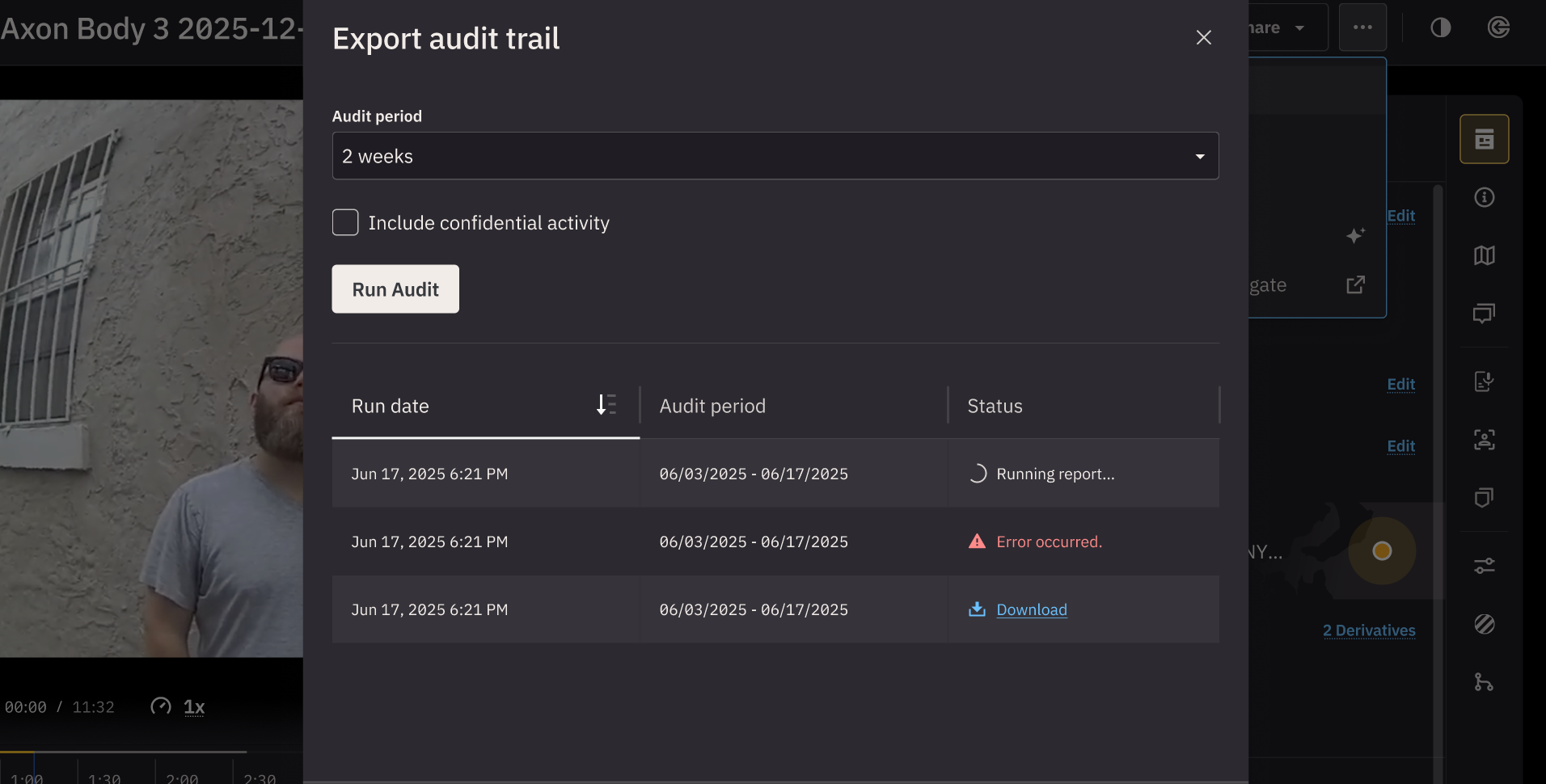
Every time someone does something in the system — whether that’s uploading, watching, editing, or sharing a file — that action is automatically recorded in a permanent activity log (also called an audit trail). The same rationale works for potential deletions of footage (which might have been accidentally/unintentionally recorded, for instance). Once any action is performed, such activity cannot be changed or deleted from the audit file. This creates a tamper-proof digital audit trail that agencies can rely on to demonstrate chain of custody in court or during review. Axon provides the tools, training and safeguards, while each agency determines sets the rules and decides how the system is used.
Think of Axon Evidence like a highly secure library. Each piece of evidence is a “book,” and every time someone checks it out, reads it, or makes a note, that activity is logged in a permanent record. The librarian (the agency) decides who gets a library card, how long books are kept, and who can access them. Meanwhile, Axon ensures the shelves are secure, the catalog is accurate, and the books themselves are locked with encryption — meaning even if someone tried to sneak in, they couldn’t open or alter a book without the proper key. And just as the library keeps an unchangeable ledger of every interaction with its books, Axon Evidence maintains a digital audit trail so agencies always know exactly who did what, and when.
 Body-worn camera accountability by design
Body-worn camera accountability by design
Axon’s body-worn cameras are designed to protect the integrity of what they capture and who/how it is interacted with from the moment they start recording through its use in the justice system. Here’s how:
Watermarks on every frame: Every video frame includes a digital timestamp and camera serial number that is embedded at the time of recording and cannot be altered retroactively.
Automatic system logging: The camera records every time it starts or stops, and logs that activity permanently.
Footage is encrypted at rest and in transit using the latest standards: This means even if someone were to intercept files, they would be unreadable without authorized keys. Combined with access controls, this makes the system highly resistant to hacking or unauthorized tampering.
Auto-uploading: Footage cannot be manually deleted from the camera. Recordings are not lost or prevented from uploading if a camera is powered off or runs out of battery. If the camera battery runs out, the video captured before the battery ran out is uploaded automatically once the camera is recharged and docked.
Video Recall: Cameras include an 18-hour forensic buffer called “Video Recall,” which allows agencies to recover footage captured while the camera was not actively recording, helping ensure critical moments are not lost, even in extraordinary circumstances.
Understanding camera assignment and user activity
Agencies are responsible for assigning cameras to officers and creating respective users within the system (even if with some generic name, for instance). When an officer changes roles, is between assignments, or no longer needs a device, they may be marked as “inactive.” This status simply reflects their current assignment — it doesn’t erase or hide their history. All past activity remains in the system, fully preserved and traceable.
If a camera isn’t reassigned right away, new footage might appear linked to a previous user. That doesn’t change the actual footage or compromise the evidence, it’s just a result of how the camera was handed over. Importantly, no user can be fully deleted, so the history of who touched what stays clear.
To make camera assignments simple, Axon offers fast and easy applications and kiosks that let agencies re-assign cameras in just a few seconds, however it is the agency’s duty to ensure cameras are properly assigned. This flexibility helps agencies share cameras quickly without interrupting operations. Even if a reassignment is missed, the evidence itself is never lost or altered. The footage remains fully intact, time-stamped, and encrypted — the only difference is how it is temporarily attributed. Agencies remain responsible for correct assignment, but Axon’s safeguards ensure the evidence itself stays secure.
 Who controls evidence retention and deletion?
Who controls evidence retention and deletion?
Agencies also set their own evidence retention policies, deciding how long footage should be stored and who can delete it. Axon’s role is to make sure the audit trail is immutable, so the chain of custody is maintained for the purposes of allowing the footage to be used as evidence on potential investigations.
Here’s how it works:
Within Axon Evidence, if a video is scheduled to be deleted after, for example, 10 years, the system automatically flags it 30 days beforehand. Once a video is set for deletion based on the retention window, it can be recovered for up to 7 days. During that window, the agency decides whether to keep it or let the deletion go ahead. This feature gives agencies more control, fewer surprises, and a safeguard against accidental loss.
Axon builds and secures the platform, but only agencies set retention schedules and define what stays, what goes, and when.
Even if some file is deleted, the audit trail remains permanently available.
 What about security and compliance?
What about security and compliance?
Axon’s systems are designed to meet international legal and cybersecurity standards. That includes:
Cryptographic protections at the source: When a video is recorded, it gets a digital fingerprint (called a Merkle tree hash) that proves it hasn’t been altered.
Integrity checks during upload: We use a tool called a SHA-2 checksum to validate upon receipt that nothing changed while the file was being uploaded to the cloud.
Independent Certifications and Audits: Beyond our own safeguards, Axon undergoes regular third-party audits and maintains certifications such as ISO/IEC 27001, SOC 2, and CSA STAR. These external checks validate that Axon Evidence meets rigorous international security standards, so customers don’t have to just take our word for it and have trusted assurance of compliance. We continue to invest in advanced strategies that keep evidence secure. You can explore our trust and compliance practices at trust.axon.com.
FedRAMP High Impact Authorization: Axon holds authorization from the U.S. Federal Risk and Authorization Management Program (FedRAMP) Joint Authorization Board (JAB) at the High Impact level for our cloud-based “Software-as-a-Service” solutions. This allows government customers to securely store and manage the most sensitive unclassified data used by federal civilian agencies.
Supporting safe and transparent use of technology
We’re proud to support law enforcement agencies around the world as they modernize how they manage digital evidence.
Axon provides secure systems, encryption, and compliance safeguards. Agencies, however, are accountable for how those systems are used — including camera deployment, access permissions, and adherence to local laws and policies. Our role is to support them with training, ongoing improvements, and transparency, so they have the tools they need to meet their obligations.
We believe the more people understand how these systems work, the more trust they build. That’s what accountability looks like, and it’s what we’re committed to.